
ios逆向小记
reveal分析图层界面,找到图层所属类,利用frida-trace hook该类进行栈回溯确定关键点,同时可以通过图层类名称来推测其是否属于webview。
·
ios逆向小记
定位关键点
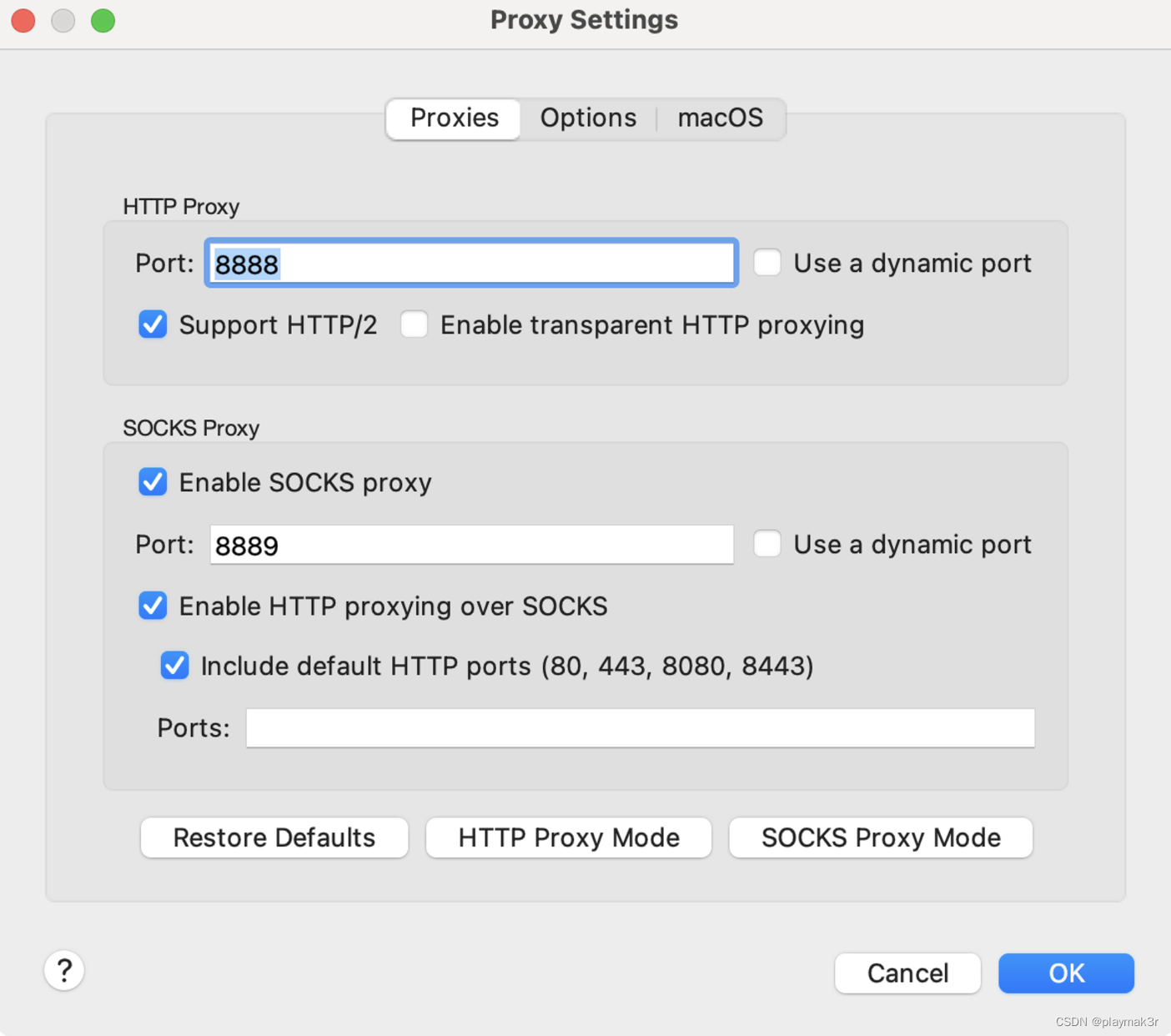
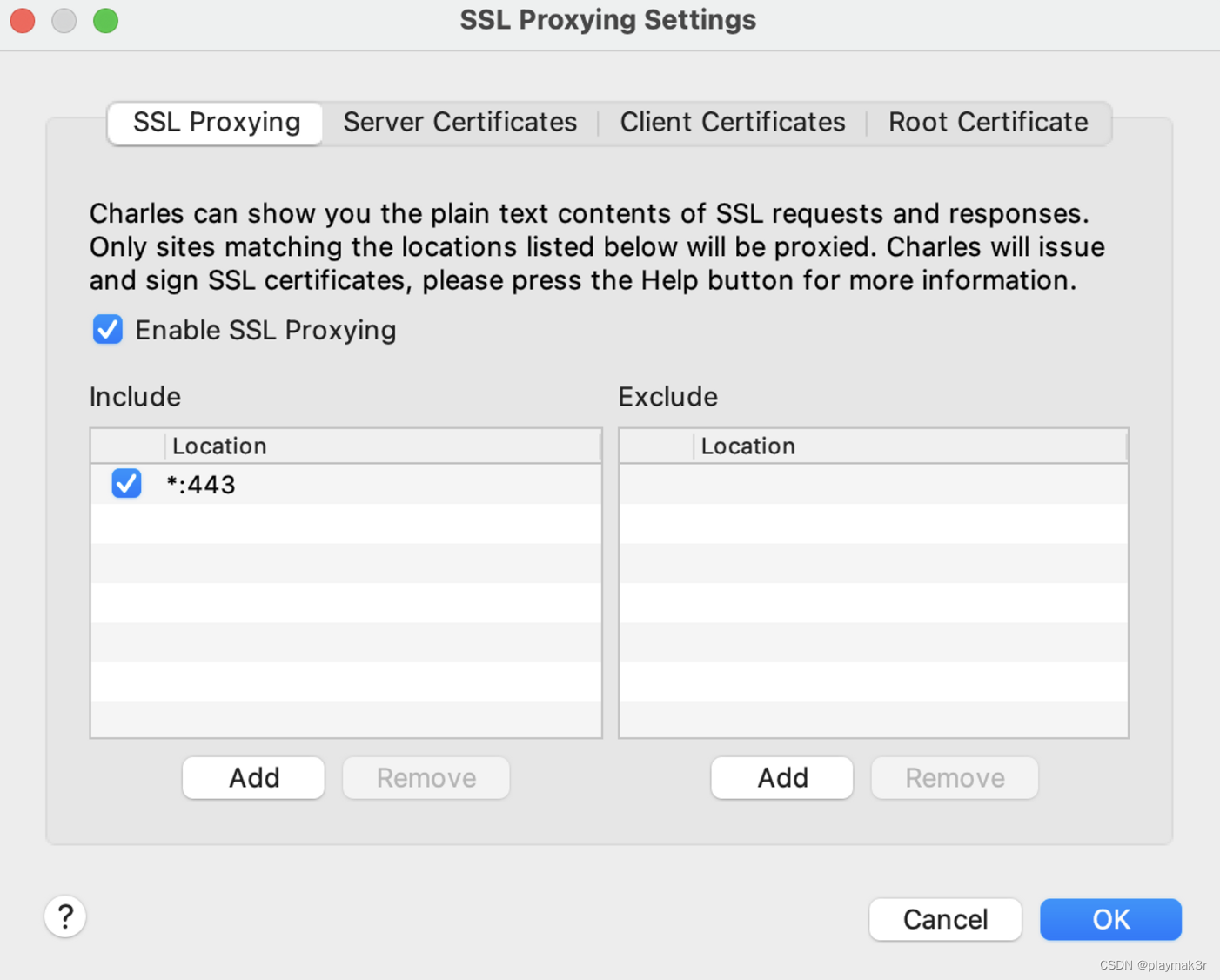
抓包
利用charles进行抓包来定位一些关键字符串,其中抓包配置如下:
reveal
reveal分析图层界面,找到图层所属类,利用frida-trace hook该类进行栈回溯确定关键点,同时可以通过图层类名称来推测其是否属于webview。
webview动态分析参考链接:https://blog.csdn.net/morris_/article/details/106778869
hook
- urlwithstring hook
var method = ObjC.classes.NSURL['+ URLWithString:'];
var origImp = method.implementation;
method.implementation = ObjC.implement(method, function (self, sel, url){
console.log("+ [NSURL URLWithString:]");
var urlString = ObjC.Object(url);
console.log("url: " + urlString.toString());
if(urlString.toString().indexOf("")!=-1)
{
console.log('\tBacktrace:\n\t' + Thread.backtrace(this.context,Backtracer.ACCURATE).map(DebugSymbol.fromAddress).join('\n\t'));
}
return origImp(self, sel, url); //调用原方法,如果不调用则原方法得不到执行
});
- 加解密函数inlinehook
function inlineHook3() {
var baseOffset = 0x100000000;
var base = Module.findBaseAddress('');
console.log('base: ', base);
var sub_1001403fc = base.add(0x100139070- baseOffset);
console.log('0x1000614458: ', sub_1001403fc);
var decode_data = 0;
var sm4_len = 0;
Interceptor.attach(ptr(sub_1001403fc), {
onEnter: function (args) {
console.log("sm4 inputdata: ",hexdump(args[1]));
console.log("sm4 len: ",args[2]);
decode_data = args[3]
sm4_len = args[2] >>> 0
}, onLeave: function (ret) {
console.log(decode_data);
console.log("decode result",hexdump(Memory.readPointer(decode_data)))
hexdump_addr(Memory.readPointer(decode_data),sm4_len)
}
});
}
- cccrypt库hook
https://r08ust.github.io/ios_cccrypt.html
静态分析
脱壳
https://www.cnblogs.com/paperpen/p/14845675.html
其他
- objc_msgsend 参数1:对象 参数2:方法名称
- AppGroup目录 /private/var/mobile/Containers/Shared/AppGroup
- NSHomeDictionary目录 /var/mobile/Containers/Data/Application/
参考链接
https://github.com/lefex/iWeChat
更多推荐
 已为社区贡献1条内容
已为社区贡献1条内容









所有评论(0)